Deploy a Wireguard service on a Raspberry Pi or VPS
23 February, 2020 - 5 min read
This article will guide you through the installation and configuration of a Wireguard service on a Raspberry Pi with Raspberry Pi OS. This guide is valid as well for other Debian-based distributions, like Ubuntu Server.
The user experience for setting up the Wireguard server is purposely similar to the setup of Wireguard server.
Getting the installation script
curl -L https://install.pivpn.io -o /tmp/install.shThis will download the pivpn installation script into a the /tmp folder. At this point you can peek into the script to inspect its content.
The next step is to execute the installation script.
Installation and Configuration
Run the script with the bash interpreter.
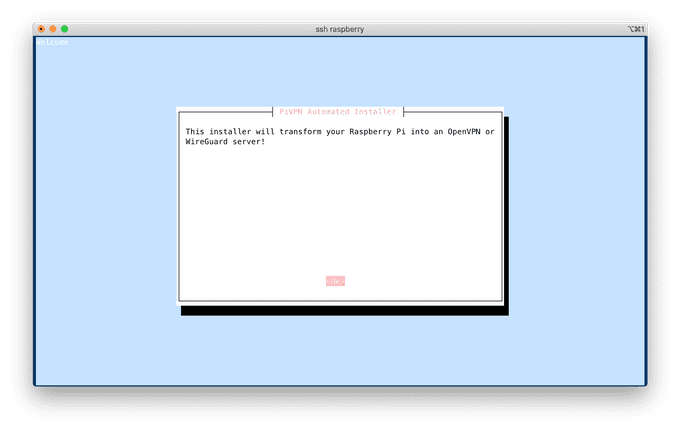
bash /tmp/install.shAfter checking for requirements, you should be greeted with:
Local IP of the server
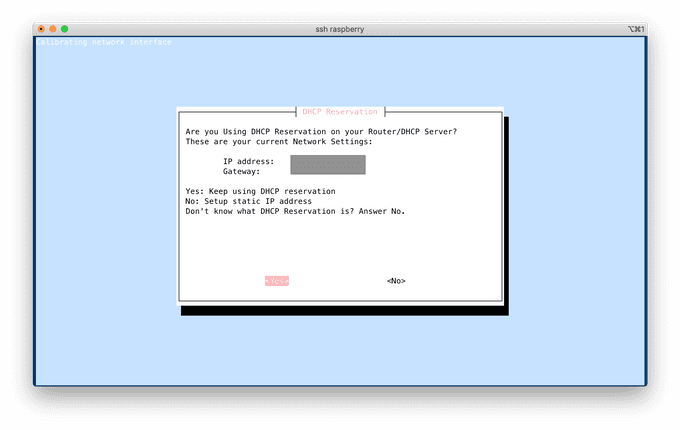
The first important configuration step is to make sure that the device that will act as the Wireguard server, the Pi in this case, has a static LAN IP. This can be done on your router, or on the device itself. In the former case, the DHCP service of your router will make sure to assign the same local IP address to your device, identified among others by the MAC address of its network interface. In the latter case, the static IP is configured in the /etc/network/interfaces file. The device would then send the requested static IP to the router, when the corresponding network interface is started.
If you have already setup a DHCP reservation on your router, for that particular device, choose "Yes". Otherwise, this is your chance to setup a static LAN IP address. Also, make sure that the Gateway address corresponds to the IP of your router.
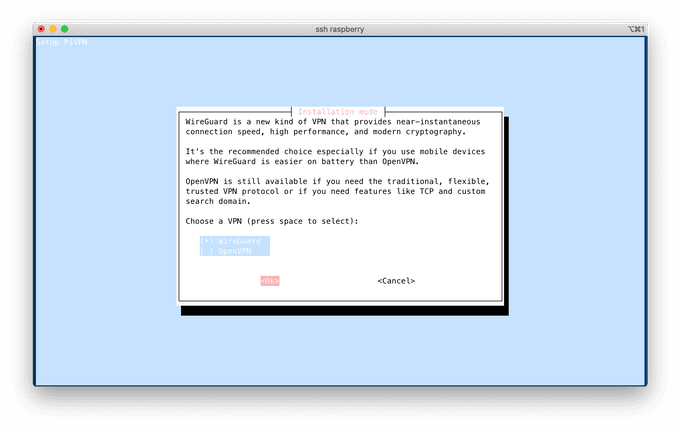
The step that follows is trivial and requires you to choose a user, who will hold the configuration profile. After that, choose "Wireguard" and go with the proposed settings on the step that follows.
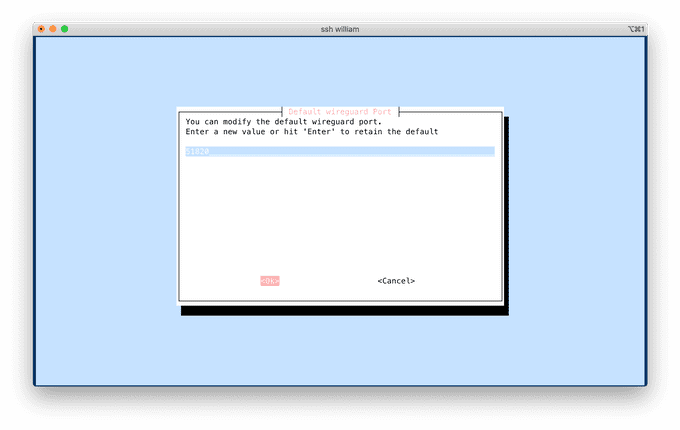
Wireguard port
At this point you have the opportunity to choose the port on which the Wireguard server will be listening to, 58120 being the default port number. Pick a value and write it down, since it will have to be allowed by your firewall, and by your router, since the Wireguard clients will connect to it from outside of your network.
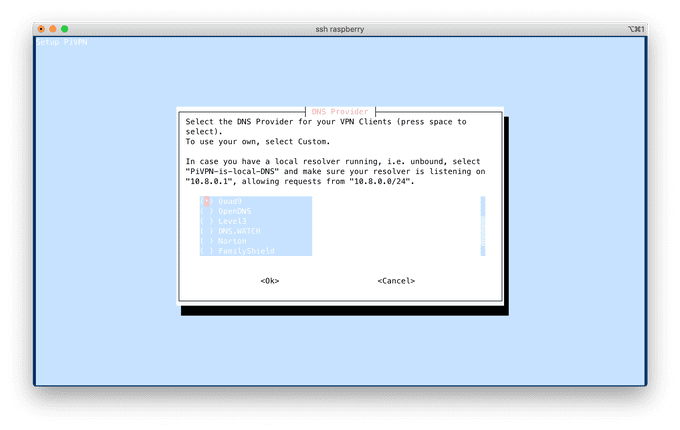
DNS server
Pick the DNS server of your choice. You have the possibility to set a custom one, e.g. pointing to your router in case it is running a DNS service.
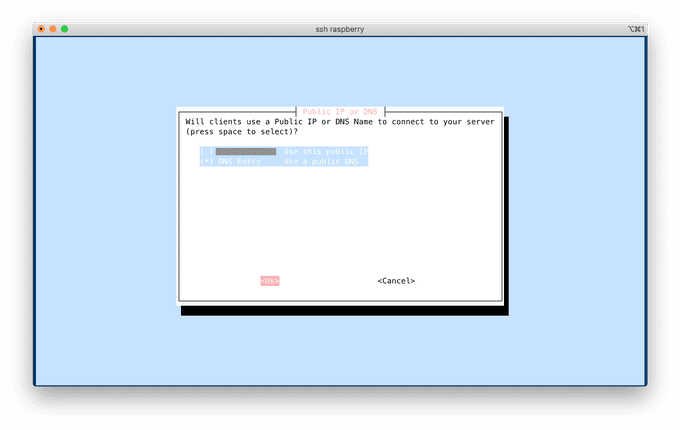
External IP or Dynamic DNS
Unless your internet provider is providing you with a static external IP that does not change, you need to enter here your dynamic DNS name, i.e. the server name that resolves to your external IP, and updates it when the latter is changed by your internet provider (typically when the router is restarted). The IP address or name that you set up will end up in the client configuration profiles, generated at the end of this guide, and will serve as the target endpoint to which clients will connect to. Setting up a dynamic DNS is left out of scope of this guide.
Enable unattended upgrades
Since the server will be listening for connections from outside of your network, it is recommended to enable unattended upgrades of security patches. This feature will make your server check for available upgrades automatically and regularly, and apply them when necessary.
Opening up the way for connections (firewall + router)
If you are using ufw as your firewall, the script should automatically detect it and add an "allow rule" on "1194/udp", assuming you have choosen that port, and kept UDP as the transport protocol. Check that the rule is indeed present:
sudo ufw statusYou can also restrict further the rule, for example if you know from which IP addresses will connect the Wireguard clients.
You should be left with the configuration of "port forwarding" on your router. Details are left outside of this guide, since router interfaces vary, but it usually boils down to instructing the following to your router, again assuming that you are using 58120 as Wireguard port value and UDP as transport protocol:
UDP connections to port 1194 should be forwarded to <local IP of your server, port 58120>
Configure a client
While the service has now been configured, we now need to generate client profiles for client devices which will communicate with the VPN server. For example, a profile for your laptop. Create a new profile with:
pivpn wg addPick a name for the client, e.g. android. This will generate a .conf file, and will save it in the directory $HOME/configs. That is the file you'll need to transfer to the client.
Tip: you can use pivpn wg -qr and pass the name of the client, e.g. android, to generate a QR code of the profile, that you can scan with the mobile app. This works over an SSH session too.
Final step
The final step is to get a Wireguard client for your client device, and import the profile previously created.